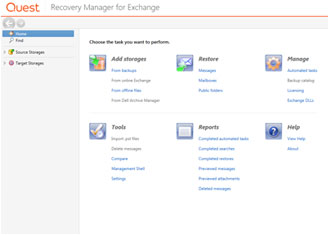
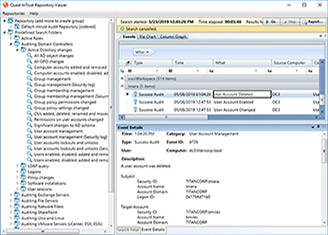
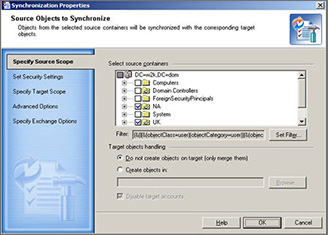
Modernize your Microsoft infrastructure
 02:06
02:06
Learn why Quest is the leader in Active Directory, Exchange, SharePoint and Office 365 with modernization solutions that help organizations get future ready and keep pace with evolving business priorities.