HI
Any one have idea how to create\add multiple owners for single AD security group(Not for DL)
is it possible with active role ? or using power shell?
Regards
Ameer
HI
Any one have idea how to create\add multiple owners for single AD security group(Not for DL)
is it possible with active role ? or using power shell?
Regards
Ameer
Active Roles has a virtual attribute for groups called edsvaSecondaryOwners.
You can populate it thus:
$MyGroup = "Some group"
$MyOwners = "CN=User1,OU=MyUsers,DC=MyDom,DC=Com","CN=User2,OU=MyUsers,DC=MyDom,DC=Com",
Set-QADGroup -proxy -identity $MyGroup -SecondaryOwner $MyOwners
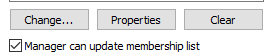
And of course you can do this in the group properties in the AR Web UI:

And of course you can do this in the group properties in the AR Web UI:

If you must use an AD attribute (rather than a Active Roles Virtual Attribute), another option is to make a group object the manager of the group. This would be instead of setting an individual user object.
IE
In the above example if both the "Owners" and "Application 1" groups had also "Manager can update membership list" checked, both UserA and UserB would be able to control membership of both groups.
IE they could
To steal Johnny's code for this example:
$MyGroup = "Owners" $MyOwnersDN = "CN=Owners,OU=MyGroups,DC=MyDom,DC=Com" Set-QADGroup -proxy -identity $MyGroup -ManagedBy $MyOwnersDN $MyGroup = "Application 1" $MyOwnersDN = "CN=Owners,OU=MyGroups,DC=MyDom,DC=Com" Set-QADGroup -proxy -identity $MyGroup -ManagedBy $MyOwnersDN
There are pro's and con's from both methods, using groups can make it hard to understand who (individually) manages each group, but the value is stored in AD (which might be useful).
Using the secondary owner means that the membership has to be controlled via Active Roles (as its a virtual attribute, so can't directly be used outside of Active Roles via script for example, without querying Active Roles, however each manager/owner is list (note that groups can also be secondary owners).
If you have a particular requirement, let us know
Cheers
Stu
It's worth noting that the contents of the AR VA are written through to msExchCoManagedByLink in AD so you could have "native" access to see all of a group's owners through that attribute. Indeed, if you check the box in the AR Web UI under secondary owners for "Secondary owners can update membership list" this permission (to add remove group members) is written through to the NATIVE AD object ACL for the group.