OK, so. So again, it's a talk, so we'll exchange a bit. We just had a talk in the room. I think most people who are in here were in the other talk as well, which was more on B2B identity management and the challenges there. Right now I think it's in enterprise and where it's heading. What are your main takeaways and maybe before we start a bit more of introduction than just saying you're at NetIQ and have a Novell legacy. So maybe you can elaborate a bit more on that.
Yeah, sure. So thanks, Martin. I'm Larry Chinski, and I'm Senior Vice President of Corporate Strategy at One Identity. So that means a lot of things when you look at different organizations.
That's One Identity. Sorry.
Yeah. Well, I was at Novell for 17 years.
I think he mixed it up saying you were at NetIQ.
Yeah, yeah. Yeah.
Sorry.
Yeah, I was at Novell, NetIQ, Micro Focus for 17 years, going all the way back to my eDirectory days. I think that's probably where I first met Martin years ago. So I run Corporate Strategy at One Identity now. I've been there for six years. And so that means a lot of things. So I run everything from our strategic marketing, corporate strategy, our field strategists. I do a lot of our demand generation bubbles up to me, as does our technical alliances. So, you know, when we look at, internally, at One Identity on what our gaps are, like what products we think we need to have to fill and complete more of an identity fabric. Martin mentioned that in his last session.
So it's my responsibility to look at different M&A targets. Do we need to buy something, build, partner with somebody, that sort of thing, to fill those gaps. And then all the enablement, technical enablement, certification, all bubbles up to my organization as well. So a lot of different pieces move up into what we call Corporate Strategy at One Identity.
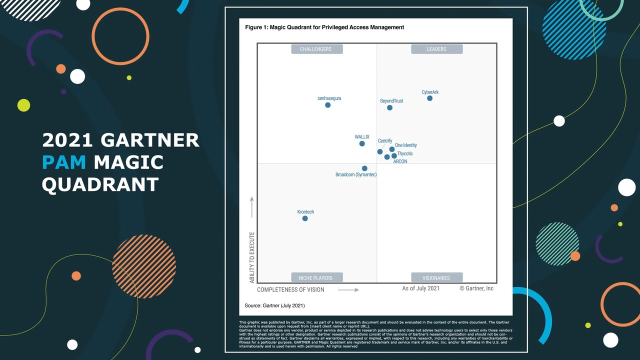
And it's really all around creating a much more unified approach to how we look at the market today. So, you know, we don't want to get into these product versus product type of things anymore since it's really everything is-- if you guys probably looked around the conference today, I made a comment on this earlier, whether it's ARCON, SailPoint, some of the others, they're all talking about the unification of identity or a converged platform.
So we've been positioning that for about the last five years. So it's really one of the trends we see in the market today based on that current threat landscape.
And so when we look a bit at the takeaways, except of that, there's a lot of identity security written on the booths, and conversions, and things like that. But what is it where you say this is really something you feel is very relevant to the, I would say, not only to the industry but to the customers of the industry? Because I think at the end of the day, it's about the customers.
Yeah, it is. As a matter of fact, and that's a good question. One of the things I noticed like when-- and just like Martin, we go to a lot of these and you guys, I'm sure too, go to a lot of these conferences, whether it's, you know, there's different organizations, RSA and some of the other ones have put these on. You know, a lot of the times what I see at the conferences are all built a lot around what I would call a cost-savings initiatives or vendor consolidation or operational efficiency and that sort of thing.
But what I'm seeing more and more in the conversations I'm having with our customers and I fly globally talking to customers and our channel ecosystem is-- it seems like and you guys can correct me if I'm wrong because you're in the space, is that there seems to be a lot more emphasis now in this space specifically around building a secure platform and security, not as much around OE and vendor consolidation. That stuff's important, but if you look around here, it's really all about security and spending money on security.
And I've always said that I thought that was the most important part of any of these individual market segments. And what's interesting about access management, for example, you'll get Okta or Ping and some of the other ones, if you look at the top four reasons why organizations buy and access management solution today, there's all kinds, but do you know where security fits, number one, two, three or four? Can anybody guess? Anybody want to take a guess?
Four. It's number four. So Access Management is, by over 2 times, the most widely deployed IAM market segment. But security is all the way down at the bottom, which is very interesting. So that means that all these other market segments are being purchased much more for the security element, where access is being purchased for the OE and efficiency. So, you know, when I look around at these conferences and these different market segments, it's pretty interesting how you see the trends start to separate, but then also come together at the same time.
Yeah. And I think for me it's also that we see that identity management is getting bigger. So you talked about vendor consolidation, which by the way, is an interesting thing. When we started, when we did the first EIC, someone said to me, you know, does it really make sense to have such a conference with over 20, 30 vendors and then they start-- the one vendor starts acquiring the other. And so you won't have a market maybe in a few years from now. I would say we probably are more in the range of-- I think we are getting closer to the 1,000 identity management vendors nowadays.
When we take all the identity verification layers, when we take all the decentralized identity startups, when we take all the other startups around, for instance, secrets management or machine identity, which is a horrible term because a machine for me makes noise and moves and is of iron and so on. And it's not just the service. But I think we can argue that would be a very separate conversation here.
Yes.
But at the end of the day, I think we see that this market is getting bigger and bigger. And on the other hand, we also learned that we need to bring together things again. So I think maybe it's also a constant fight of consolidating versus adding things to the overall picture.
Yeah. Yeah. And there's a separation between-- Martin, you and I just had a webinar on this topic very similar, what, about a month ago, we did that-- But I mean, there's a difference between convergence and consolidation. And I think you're right, probably 1,000 identity vendors when you look at all the-- well, shoot, just IGA probably has eight or nine segments that fall under it. You know, Access has MFA and that sort of thing. But the consolidation is kind of like the technology components coming together, and convergence are like the companies coming together to form a whole new space there.
And I think my colleague Alejandro currently is working on, I think on the leadership, on access management, and I think he has almost 50 vendors in the ratings.
Yeah.
Alone in this sub-segment, it's one of many segments here. So it is we have a lot. And I think exactly the point is so consolidation versus convergence. I think the very important thing is to homogenize and to unify the initiatives you're taking. So getting away from, I do this here, a bit IGA here, and then I have a totally separate access management initiative, et cetera. So honestly, if in your-- who is in an organization where identity and access are still segregated, organizationally?
So you don't need to raise your hand because otherwise I need to blame you.
We won't call on you. That's OK. We promise. At least I won't, Martin might.
But it's very clear to me it doesn't make sense. And the thing you definitely can quote me on, if Entra ID is not in the hands-- and if you have Entra ID, it's not in the hands of your IAM department, then something is wrong. So Entra ID is an access management tool, and there's absolutely no discussion about it. Entra ID must be owned by the Identity Management Department, for instance. We can argue a very little bit about the old Active Directory due to a legacy aspect, but at the end of the day, even there I would say move it over. Serves a lot of problems.
Yeah, I think you're exactly right. Matter of fact, we were just having a conversation with one of our customers on this today, and I think we had Ian [INAUDIBLE] in the booth. We were talking about that very thing on. You know, I think Microsoft has it really figured out when you look at a platform, what they're doing with Entra. But some of the subcomponents, like you said Martin, I think are just, they don't, it's a separation that occurs there.
Yeah. And we need to fix some of these things. So we're in, I think, in a constant evolution and we need to understand this is one thing. I think this was a lot of the thought around when we came up with the identity fabric idea several years ago to say, so basically when we started this, it was basically stepping back and saying, so why do we do this stuff? Why do we do identity management? At the end of the day, the purpose of identity management is that everyone and everything have a secure, seamless, well-governed access to every service.
This is basically the job of identity management. So that someone, something can connect to a service under controlled conditions, so to speak. And that's where everything starts. All the other things we are doing, we are doing to enable this. So we invented IGA because we learned we can't give everyone full access to everything, logically.
Yeah. Well, as a matter of fact, I had dinner last night with, I think I saw, there is [INAUDIBLE] over there from [INAUDIBLE] and Gerald. And we were talking about, this is going back and dating myself again, I think 1997, when I actually wrote a little hook using Microsoft Access. If you guys remember Access, if you're old like me. Using Microsoft Access, it created a hook from Peoplesoft, which was our HR tool at that time, to automatically create when somebody got hired into the organization, that ID down in our NT domain. It was not Active Directory then, it was down in our NT domain with role assignments and rule assignments that I could place them into different departments.
And that was kind of like our first step and it was a manual thing. But really what that all that was, was me writing a hook to make my job easier because I ran the corporate network operating system at the time, and I did that to make my job easier. It had nothing to do with security. It had nothing to do with protecting anything. It was, now I don't have to spend half my day creating IDs and different accounts anymore. So it's evolved into this complete, like you said, Martin, strategic initiative now.
And it's still fascinating to me, too. So I have I have to admit, I did a lot of-- I wrote books about Lotus Notes Domino. I wrote for many years. I wrote a monthly newsletter inside Lotus Notes Domino. So it's not that I'm negative on the tool, but nowadays it's, for me, still sometimes fascinating to meet an organization which says, OK, we still have it in our Notes database. It still comes from a Notes database, and that shows also how long these things sometimes exist. At least, you set access in our dBase.
Well, dBase would have been my college days, so I'm not that-- maybe a little bit older. FOXPRO. You didn't say FOXPRO either.
Yeah, exactly. So it can be even worse always. But what I really see is still these things around and clearly we need to modernize these. We need to move to a state where we are more flexible because these things tend-- actually they are always broken already. It's just that we try to put enough gaffer tape around it to keep them survive until we can do things differently. But maybe back to, to the things where you also see what is changing, what is evolving in this industry? What are the things where you feel they are-- they will be-- they are super important maybe for the audience to look at because they will change the way we do things in identity management.
Yeah. And you know, one of the things that we talk about quite often is the use of AI and hyperautomation tools. And, you know, when you look a matter of fact, I added a very short segment in my session a couple of days ago, I think it was on Wednesday. Been here all week, I forget what day, what days are what, but--
Friday is today.
Yeah, OK. That's good. I think my flight's tomorrow. But yeah, so one of the things that we talked quite a bit about at One Identity is the use of generative AI, not only from an attack perspective, but how you can use AI from an identity perspective along with hyperautomation. Now when we look at how this attack surface has widened over the years, there's kind of like four reasons that I like to talk about in depth. And that's the large remote workforce now that really came on strong around COVID. You know, cloud computing, and not necessarily cloud like goods and services in the cloud, security tools being moving to moving to the cloud as well, like IGA as a SaaS, PAM as a SaaS, et cetera.
And then, you know, the other one is this lack of-- this big shortage of cyber skills. So we're finding a lot of our customers taking 18 months to find somebody who's really qualified to do these type of things. So they invest in AI and hyperautomation tools. The problem is, those hyperautomation tools create themselves digital identities which rely upon the credential managers inside of the hyperautomation tools software for security protection, which really, quite frankly, is not all that great. And so we need to look at how we can leverage IGA tool or IAM tools to basically suck that out, push that into your IAM platform and then provide a security mechanism. So you're actually using your IAM platform to provide security for the AI and hyperautomation that we see in the market. Things like bots. You know how bots can run around and--
We've got companies, Martin, believe it or not, that don't have an IGA tool. They're actually using bots to run around, create, modify, move. So joiner, mover, leaver functions are being done by bots in the organization, hundreds of them, with no security behind them, which I find quite fascinating.
I like the bot idea. I don't like that much the no security aspect on that. So the bot idea is not that bad, I would dare to say. I think one thing here also is where I believe there's a very concrete potential for-- especially for vendors who serve multiple areas. So one of the-- so when I take a look at identity management and would have to list the three biggest challenges that regularly pop up, then it's recertification. Sure, no doubt about it. I'm still looking for the one organization globally that says, hey, my departmental managers love recertification. They want to do it again and again and again. I still didn't find it. So something is wrong here.
Role projects also tend to be a bit challenging. And onboarding, application, onboarding. And I believe we have, for instance, a very big potential of utilizing GenAI to get to a much higher level and much higher efficiency in application onboarding and automated application onboarding across all the pillars of IAM. Because when we have an application, it's not just onboarding it on IGA, it might be the most tricky part, but it's onboarding it on PAM, it's onboarding it on Access management.
The latter two tend to be a bit simpler. But anyway, I think in an ideal world, our agent or our bot or whatever it is, does it for us.
Yeah, yeah. And it's definitely, and I don't mean to be negative against bots because I think they do have a very important place. It's just the security element behind that is something that we sometimes overlook what we have to do. But yeah, the application onboarding I agree with. As a matter of fact, it sounds like it would be very difficult to integrate application onboarding with an IAM platform, but it's really not. And that's something that we do at One Identity quite often. And there are tools out there that automate that process as well. And so I think, Martin, you're right on that. That is something that can be leveraged.
I once read that an effective IAM platform can resolve like 55% of those types-- whether it's GRC or some other risk component or application onboarding. So it's really amazing how much more you can do from a security angle with that than [INAUDIBLE].
Yeah, and I think that this is one of the areas where I feel that AI can be extremely helpful. I think it's also-- you talked about the skills aspect. It can really help doing things easier. Also, again, in onboarding, when you need to onboard to a certain specific platform, then the guidance that can be provided that way. So how do you do it? What is the next step? Et cetera.
Having maybe prompt books that guide the people through that, through the things which need them still to be done manually. That's a great area for that.
Yeah, I agree. As a matter of fact, you know, to me it's almost like the next generation. You guys have all probably seen IGA platforms that have, I'll call it like a modeler inside of that. Where it can go out and look at, show me 20 other people that have similar roles or similar functions. I want to give them the same access as that. You've probably seen that. So this is almost the next generation of that where AI can step in and kind of resolve.
Yeah, and maybe do it a bit smarter than--
Exactly.
--than just saying give me the same access as my peer who has collected this access over the last 16 years and probably only needs 2%.
That's right.
I think that would be then the smart solution for that.
Right.
I think another area is processes, workflows, all that stuff where it's also something we see more and more approaches on using AI and building this, which if I were a cynic, which I am, factually--
I don't believe you.
Yeah, that would be maybe something which is also very helpful because still the vast majority of vendors in the space doesn't come up with, this is the complete, very documented, well described process framework for IGA, which you can use to start with. So in many cases, it's, yes, you have a technology, you may have some elements of workflows, but really it's a perfect, you know, process framework with wonderful whatever. EPC diagrams and stuff like that, rarely found. And so maybe AI can fix what vendors didn't do.
Yeah, I think the opportunities for AI, especially when you look at an overarching IAM framework or really kind of limitless, there's so much. As a matter of fact, I just started getting-- you guys use Wikipedia and stuff like that. I see that they've incorporated AI into some of the search results that you get there. So I think that being able to plug that into what you're doing from a security angle, that's where it can be really most helpful.
Yeah. So by the way, don't hesitate asking questions.
Yeah, sure.
So you have us here. You can ask us questions. Maybe Paul has questions from the online audience.
And I do have some questions, too, that I want to ask the audience.
OK, then you ask-- So if the audience doesn't ask questions, we ask to the audience.
Yeah.
OK. Fair deal, I believe.
Because I love gathering intel from the most important people in the audience, are the customers.
Are you going to pick on someone?
No, no, no, no. I'm just going to ask a general question. No, I'm not going to pick on someone. No, I wouldn't do that because I know it's like to sit out there and get asked.
I know couple of people in here so I could pick some.
[LAUGHTER]
So anyway, what's your question?
Well, I'll tell you, here's a question I get. And you know, One Identity and several other companies out there that have-- So I've worked for a publicly traded and publicly owned companies and privately owned companies. And one of the things from private companies is when you meet with the board, they always-- you've got a bunch of very super smart people on the board of directors that are on the private equity firms, but they've never typically run a company. So they're very interested in what's in the market and what you're telling them and that sort of thing. And so they ask a lot of the same questions, but one of the things that they ask a lot and that I like to do a lot of research on because at One Identity we like to peel apart why these trends are happening and things like that.
So one of the questions I like to find out, like I said, every one of these IGA and PAM vendors you see today are talking about the platform and the unification, the convergence, consolidation. So one of the questions I get asked a lot of times from different PE firms are, how are the customers that you see today and organizations, are they still buying in a fragmented fashion? Like if they need PAM, they buy Pam? If they need IGA, they buy IGA? Are they looking at things holistically now?
And for me, when I look at every single vendor is talking about convergence and every single vendor is talking about unification, there's a couple of things that tells me, number one, when we look at how these breaches are occurring now, and I talked about this Wednesday. They're targeting the identities specifically. And they're targeting them because they're very easy to target. Now they're out there, they're on their own. They're not being protected by dual layer firewalls and content filters and network segmentation and things like that.
So the way these breaches are occurring is, they're sweeping in between the gaps of those segments, basically kind of stealing the identities. I talked about this Wednesday, where the AT&T breach, 74 million identities were stolen, then pushed up on the dark web. Well, they're pushed on the dark web so they can be purchased by hackers who want to try and then pump them into an organization. So my guess, my question for you, kind of setting up the framework of it is--
Finally the question.
Yeah, are you guys--
It's important--
I also was waiting for it.
It's important to set up the framework before because the question may not make sense if you don't. But are you customers out there, organizations, anybody can raise their hand, are you looking at things more holistically now, from a more of a platform perspective and a true unification and security framework or are you still looking at it via PAM for PAM, IGA for IGA? How are you guys looking at it?
I think your question for raise the hand is a relatively difficult. So I would limit it to are you looking at this more holistically today, question mark.
Yes.
If yes, then raise the hand. If not, then leave it down.
All right. So we do have a-- OK, good. What I found is, it seems like about it went from 0 like two years ago, to my experience in the organizations I talk to is about 30% roughly. Are saying, yeah, you know, this makes a lot of sense. Now, everybody agrees it makes sense, but sometimes it's harder to--
What we see is really we see a lot of organizations picking up this identity fabric idea, at least from a conceptual perspective, to have a very holistic view. Not necessarily from I buy everything from the single vendor, which is also sometimes tricky because the time frames, you know, you won't usually rip and replace everything, but you do whatever IGA is here and then it takes you a while and then three years later you focus on the next big project. So this is also usually very, very split over time.
But maybe going back to Paul because I also will need to run upstairs.
Yeah, OK.
Thanks, Martin. Yeah, I know you've got to run off to another session. So I think we'll wrap it up here. I'll let you get upstairs. But thank you so much.
Thank you, Paul. And Martin. Thanks to these two guys. They were the-- yeah.
[APPLAUSE]
You know, Martin, right before Martin goes, I think I talked about this with Paul yesterday that, you know, Martin and his team were the first ones that really created a survey around this concept of identity fabric. And that was, what, three years ago, four years ago?
Almost six, I believe.
That long ago? Yeah. And now--
It was BC before Corona.
OK. OK. Yeah, BC. That's right, before corona. Now you see a few others doing that. So Martin and his team have that, have it figured out, I think. Kudos to you, Martin. Yeah.
Can you imagine what Larry's energy levels were like on the first day? This is what he's like on the fourth day. Wow.
Yeah. All right. Good, thanks, Martin. Good to see you again.
 24:11
24:11