May 23, 2019
1 PM ET
Implementing Identity and Access Management universally across multiple IT infrastructures and software platforms is a major challenge for any organization. IAM implementation is no longer about promoting efficiency during…
Implementing Identity and Access Management universally across multiple IT infrastructures and software platforms is a major challenge for any organization. IAM implementation is no longer about promoting efficiency during…
The KuppingerCole Leadership Compass reports provide detailed, independent reviews of the markets and key products for both the Privileged Access Management (PAM) and Access Governance (AG) market segments. One Identity is one of the only vendors to be…
One of my favorite classic holiday movies is Elf. It has several great rules to live by including, “gum on the street is not free candy” and “a peep show is not getting to look at your presents early.” But one of the one of the…
Upgrade from Identity Manager 6.x - Synchronization
Welcome to the first installment of our Upgrade to Awesome blog series, in it we'll take a look at the performance boost in version 7 connectors. This is important to understand as we prepare for the…
Identity and access management (IAM) is often a challenge for companies, with inconsistent and labour-intensive processes. For Swiss Post, the national postal service of Switzerland, IAM was a drain on resources because the organisation lacked an automated…
Date: Tuesday, January 24th at 11am PT / 2pm ET
Today, more than ever, organizations must address the proliferation of cloud-based applications and digitally transform their business to stay ahead of the competition and meet customer’s demands. While…
BHF-BANK achieves 40 percent faster approval times for systems access and cuts administration time on identity management by 20 hours a week.
BHF-BANK, headquartered in Frankfurt and part of the French private banking group Oddo & Cie, has been catering…

For many organizations, compliance with data security standards doesn’t seem to be getting easier. Compliance efforts often compete with projects that address information security threats and vulnerabilities, and these efforts often lose out in the battle…

While relatively a newcomer to the IT compliance scene, PCI DSS has been mandated by all members of the PCI Security Standards Council, including Visa International, MasterCard Worldwide, American Express, Discover Financial Services and JCB International…

Using the user, group and role-based management features of payment and business applications that accept cardholder data or sensitive authentication data is not enough to secure your data and ensure compliance with PCI DSS requirements.
The set of system…

Digital Transformation of business is unstoppable. It affects virtually all industries. The IoT (Internet of Things) is just a part of this transformation. Organizations that do not adapt to the transformation are risking their very survival. Furthermore…

A common misconception is that Digital Transformation is limited to certain industries, such as the ones supplying “smart homes” or “smart cities”. This is wrong. In fact, nearly every organization is impacted by Digital Transformation. Prominent examples…

Many people associate Digital Transformation with connecting things – the IoT (Internet of Things) as the quintessence of Digital Transformation. Connected things are part of the transformation, but it is about everything – business models, services…
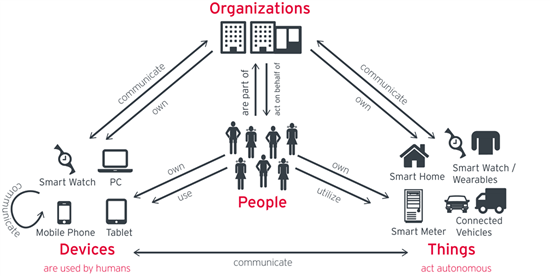
Digital Transformation adds billions of connected devices and things to what we already have in place. Therefore, we must learn to manage and thrive with the complex relationships of new organizations and their systems, devices, things and people
It…